Everybody recommends using strong passwords. However, it’s not possible to remember all passwords when you are following all the recommended rules. There are many passwords managers but usually, they are paid, not so protected or without a guarantee that the company cannot access the data. In this article, I would like to show you a highly secure and almost free way on how to manage personal passwords.
Credits Before We Start
All advice in this article is based on one Czech article on Vodnický blog. This blog has Patreon account, and you can support the authors.
Strong Passwords are Essential
You will probably know all the following recommendations on how to create a strong password because these tips are in almost every sign-up form. However, it’s good to mention these recommendations also here.
Every password should:
- Be generated to avoid using dictionary words
- Have at least 12 characters
- Be composed of letters (lowercase and uppercase), numbers and special characters
- Be unique (do not reuse a password for different accounts)
- Be changed after one year
KeePass as Password Manager
I’ve already mentioned there are many passwords managers but most of them are paid, not supporting safe two-factor authentication and mainly you don’t know how passwords are stored and who can really access them. However, there is one open-source manager that can work for all our needs called KeePass.
KeePass is not the best solution in case you are using it as it is. This project has a big community, plugins, and forks which have a much better user experience. First, you need to download your KeePass client. Basically you can choose one from this list, but I would like to recommend KeePassXC because it’s multi-platform.
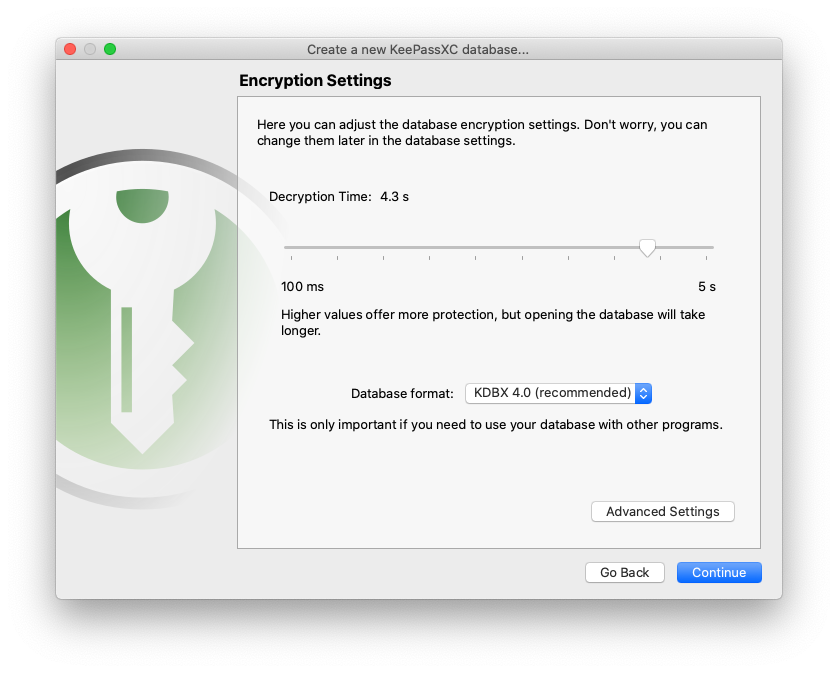
Once you download and install your KeePass, you can create your first password database. You will be asked about some encryption settings and it’s advisable to choose the recommended options and the best combination of user comfort and safety.
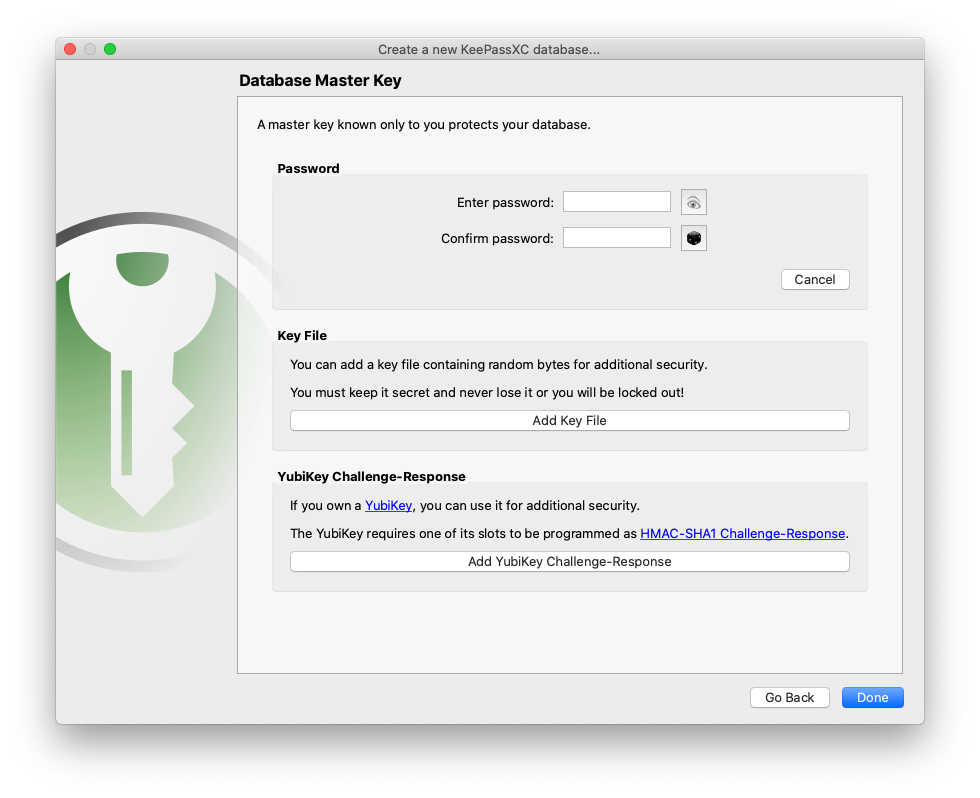
The last step for creating a database is database authentication. Let’s wait with this step for now.
YubiKey Instead of Master Password
What is the usual authentication way for other solutions? Basically, there is a password and you can add two-factor authentication with short-term codes on a mobile device (SMS or generators). Is it safe? Do you know how your mobile applications work in the background? Are you sure they cannot access these short-term codes?
However, don’t be scared because we have a solution called YubiKey NFC 5. This USB key supports dynamic verification based on challenge-response. You create keys as many as you need and the only necessary thing is a secret hash string that should be stored nowhere. This USB key contains a hardware button that needs to be pressed every time you want to access the database. That complicates finding a correct combination of secret values by some automated script. This YubiKey is also the only financial investment necessary for this approach.

In the last section, we ended up in a database authentication. We already know we want to use YubiKey with challenge-response protection and it’s recommended to use some master password, but we don’t have to choose some strong password because the database is already protected by YubiKey.
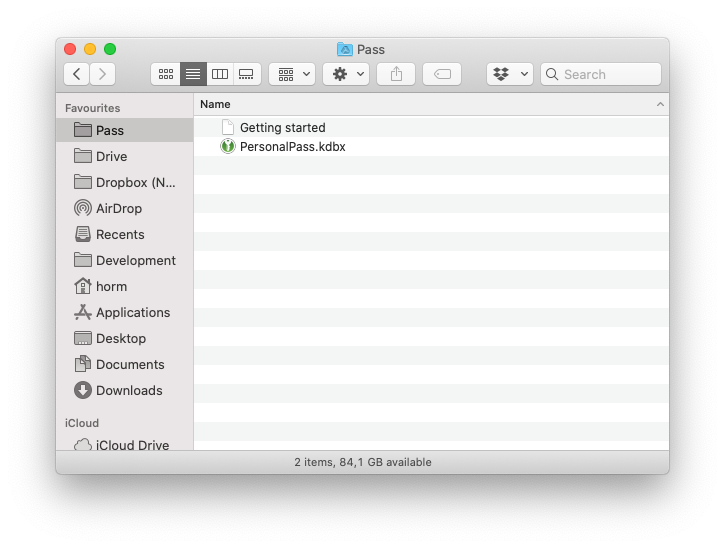
Access from Everywhere and Backups
The setup described in the section above allows us to use any existing cloud storage such as Google Drive, Dropbox. The author of the blog is also saying that the file theoretically can be public.
I’m using Google Drive with a separate Google account and Google Backup and Sync Tool. I’m accessing the database from 2 devices and it works with no problem. I’ve also created a guide for how to access the database without not remembering any password or secret key. This guide is divided and shared with people I trust. In the worst-case scenario, they can compose the guide and access the database. Google also send notification emails about new logins.
The main disadvantage of this approach is the sharing of a database between many users. Google backup tool will automatically update a database but editing the database by two users at the same time can produce some lost changes. Please consider that in case of using this approach for teams.
Last but not least:
- Do manual or automated backups of the database.
- Use Chrome plugin for inserting passwords.
- In case of access on the phone, be sure it’s secure.
This article is based on the existing one, so support the original author on Patreon if you found this article useful. I don’t guarantee this bulletproof way of storing personal passwords, but I think it’s a very secure way. What do you think? Are you going to implement this way? Do you have ideas on how to improve this approach?